We’ve attempted to summarise the two recent (September 23) cyber-attacks that made the headlines in the context of cyber-risks, ethics, and the decision conundrum when dealing with major incidents.
Cyberattack 1: MGM Resorts
MGM Resorts International is a global hospitality and entertainment company with a portfolio of 29 hotel and resort properties, including iconic brands like Bellagio, MGM Grand and Mandalay Bay. The company operates various resorts, casinos, and entertainment destinations. The estimated annual turnover is USD 15.38 billion.
Based on information from various news sources:
The financial impact of this attack was substantial, with a $100 million hit to the third-quarter results.

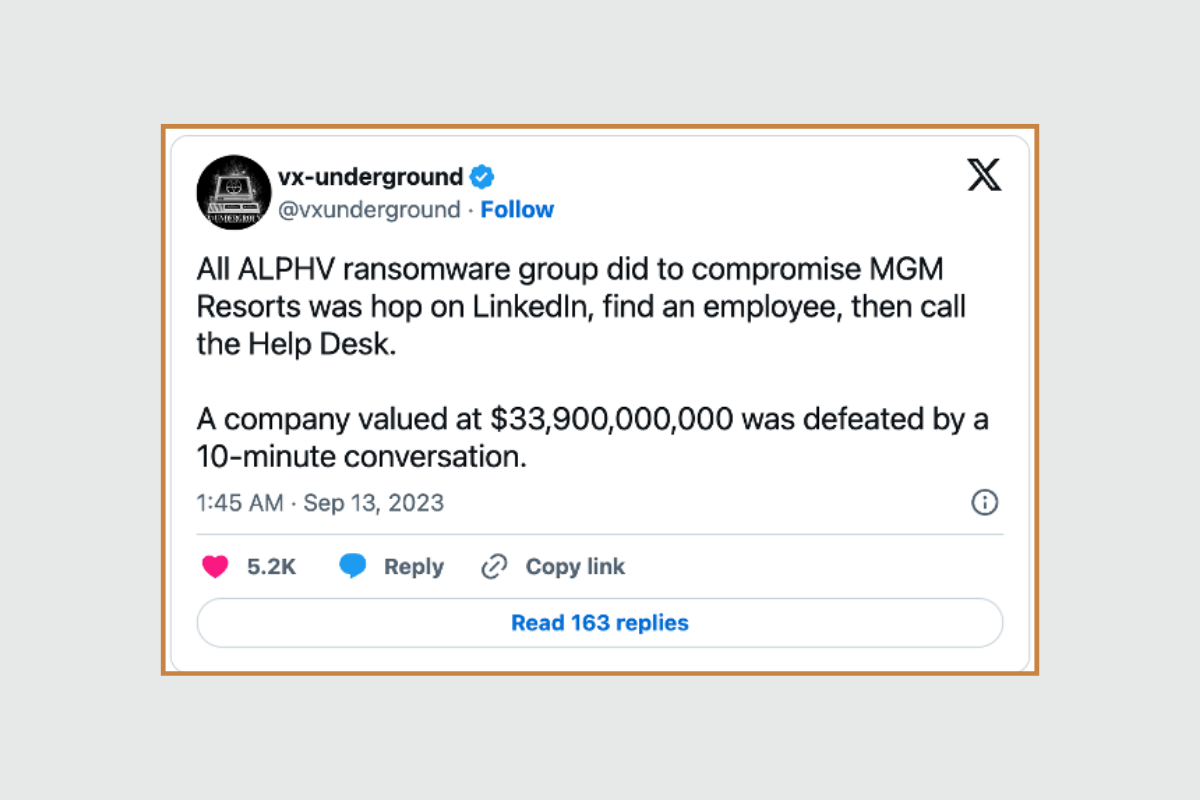
The perpetrators
- The hacking group “Scattered Spider” is suspected to be behind the attack using ALPHAV Ransomware as a Service.
- Also known as Roasted 0ktapus, UNC3944 or Storm-0875.
- The group members are believed to be English-speaking, are aged between 17 and 24, and communicate through a Telegram channel.
- Believed to be based in Europe and the USA.
- Scattered Spider specialises in social engineering attacks.
- Due to their fluency in English, they can convincingly carry out methods like smishing and SIM swapping.
- The hackers are adept with vishing, and they often exploit third-party vulnerabilities.
A further $10 million was spent on one-time expenses for risk remediation, legal fees, third-party advisory, and incident response measures.
The methodology
- Scattered Spider researched MGM and found employees’ information on LinkedIn. By impersonating them on a call with the outsourced IT Helpdesk, they managed to reset the MFA for the account.
- The attackers created persistence in MGM’s network and gained control over critical systems, including Okta and the Microsoft Azure cloud environment.
- This allowed them to exfiltrate terabytes of data from MGM’s network.
- They deployed their ransomware (ALPHV/BlackCat), severely disrupting MGM’s operations and services.
The response
- MGM’s decision was not to pay the ransom.
- The Okta sync servers were terminated, leading to the termination of the threat actors’ initial access.
- As the hackers had persistent access to Azure, all services had to be shut down and rebuilt.
Lessons learnt

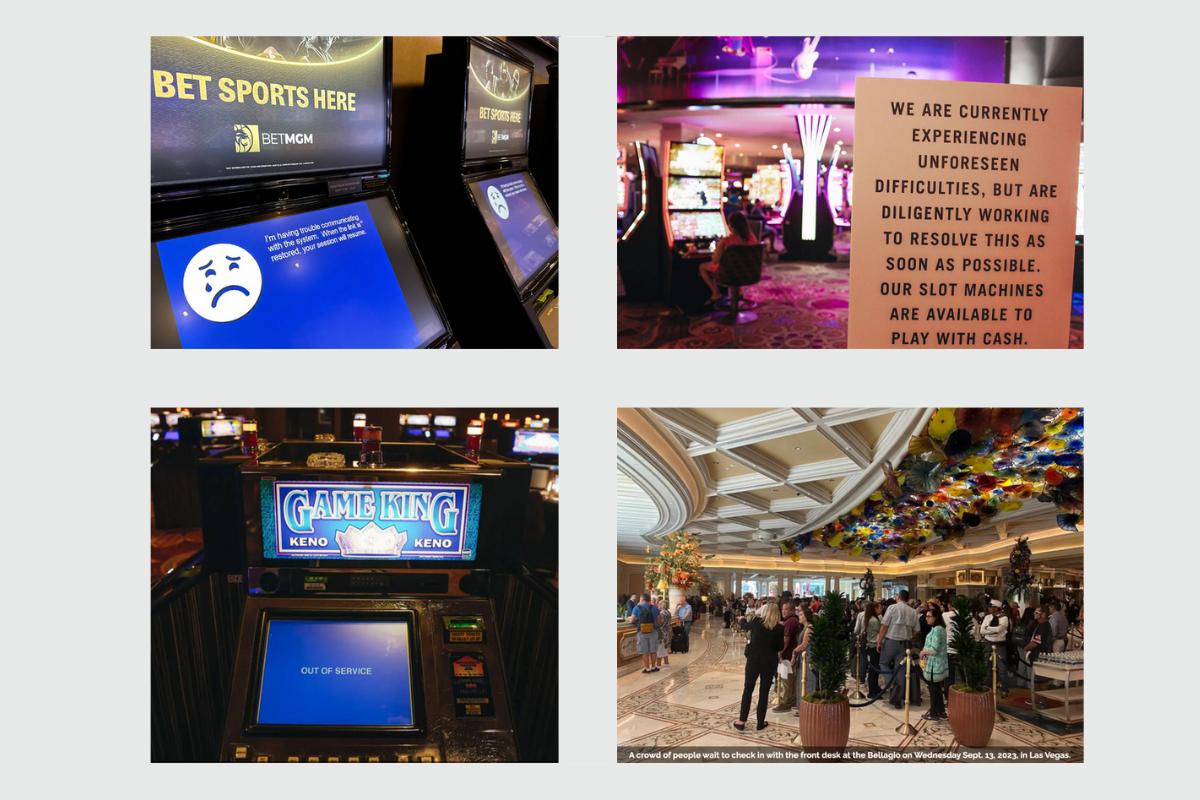
The images above (courtesy reviewjournal.com) provide a sense of the impact.
Cyberattack 2: Caesars Entertainment
The initial ransom demand is considered $30 Million, negotiated down to $15 Million.



